Resources
Featured Content
The Total Economic Impact™ of M-Files 2023, a commissioned study conducted by Forrester Consulting on behalf of M-Files, determined that M-Files delivered nearly a 294% return on investment (ROI) over three years to organizations by streamlining processes and driving efficiency.
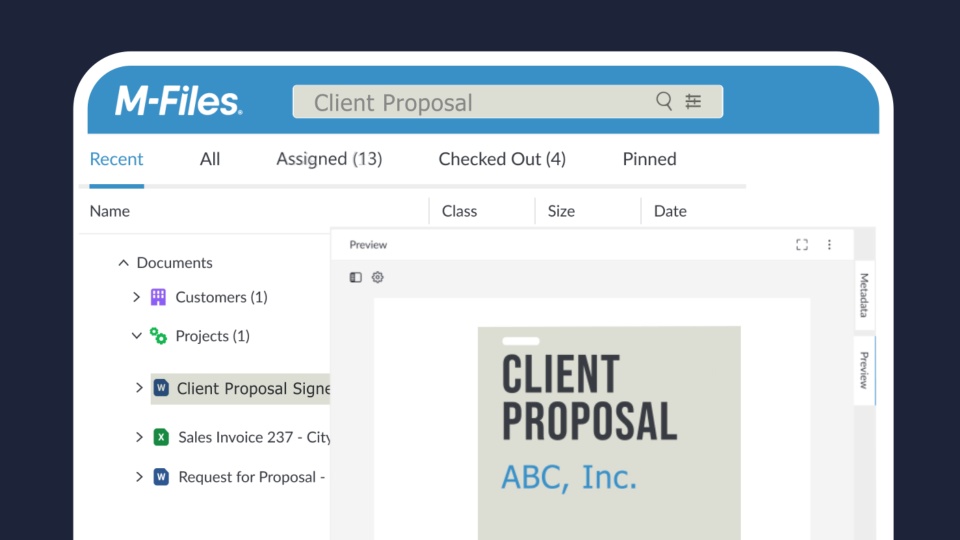
See M-Files in Action
Seeing is believing. Schedule a demo to learn more about simplified search, automatic workflows,intutive user interfaces, and built-in integrations with existing applications and file systems.
Case Studies
Case Studies
Aluflexpack
Case Studies
Washington University Investment Management Company
Case Studies
FVCbank
Case Studies
HUMANEXX & Hanselmann
Case Studies
TTI, Inc. – Europe
Case Studies
Van Rhijn Bouw
Case Studies
Finnfund
Case Studies
Schera
Case Studies
ello communications
Case Studies
St Paul’s Collegiate School
Case Studies
Syntal
Case Studies
Indara
Case Studies
Farmers Trading Company
Case Studies, Video Case Studies, Videos
Innisfree
Case Studies
HL Technology
Case Studies
Posti
Case Studies
DUO Collection
Case Studies
Charles River Laboratories
Case Studies
Valeo Financial Advisors
Case Studies
Freeze-Dry Foods
Case Studies
Newman Women’s Shelter
Case Studies
HEB Construction
Case Studies
Norco Co-operative Limited
Case Studies
Kavanagh
Case Studies
Banijay
Case Studies
Natsure
Case Studies
vem.die arbeitgeber
Case Studies
Hotel Schweizerhof Bern Ag
Case Studies
IKM Ocean Design
Case Studies
Crowe UK
Case Studies
Anderson Construction Ltd
Case Studies
Federal Realty
Case Studies
Burra Foods Australia
Case Studies
E tū Union
Case Studies
Himmelwright, Huguley & Boles
Case Studies
Newsec
Case Studies
ETHRA
Case Studies
Wijbenga
Case Studies
Vigor Works
Case Studies
TEAM Industrial Services
Case Studies
Tampere Adult Education Center TAKK
Case Studies
Stearns Bank
Case Studies
SRSI
Case Studies
Southern Hills Title
Case Studies
Austbrokers Countrywide
Case Studies
SATRA Technology
Case Studies
Roal
See M-Files in Action
Seeing is believing. Schedule a demo to learn more about simplified search, automatic workflows,intutive user interfaces, and built-in integrations with existing applications and file systems.
Videos & Podcasts
Case Studies, Video Case Studies, Videos
Innisfree
See M-Files in Action
Seeing is believing. Schedule a demo to learn more about simplified search, automatic workflows, intuitive user interfaces, and built-in integrations with existing applications and file systems.