Document Security Systems for Access Control and Compliance
Protect Sensitive Data with Document Security Systems
Your business documents contain a great deal of valuable data and sensitive information – which is why they’re the target of cyber criminals and malicious actors. As the volume of documents you create, use, and store continues to rise, so too does the risk of a breach. Achieving superior security requires a multilayered approach that combines awareness training, effective practices, and document security systems.
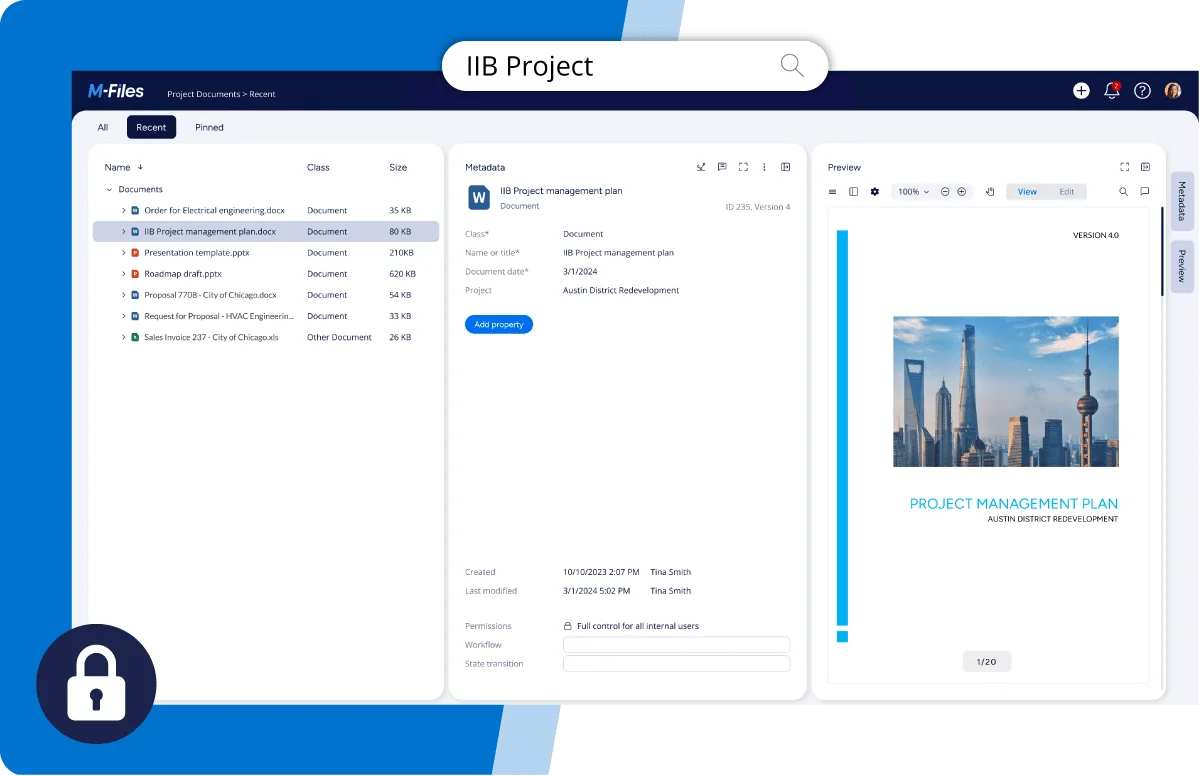
Document security systems are technologies that protect documents from theft or unauthorized access. From encrypting files to controlling access, these systems automate the process of applying a variety of protective measures to minimize risk and fend off attacks.
As a next-generation intelligent information management platform, M-Files offers advanced, AI-powered technologies that can play a critical role in designing a superior document security system.
More Control Over Documents and Processes
Keep your data secure and enforce policies throughout the organization with M-Files.
The M-Files Impact
There are huge inherent risks in creating, using, sharing, and storing documents. From cyberattacks and breaches to data leaks and malicious insiders, the security of your documents and the sensitive data they contain is constantly under threat.
There are three critical considerations when designing document security and risk management solutions for addressing these threats.
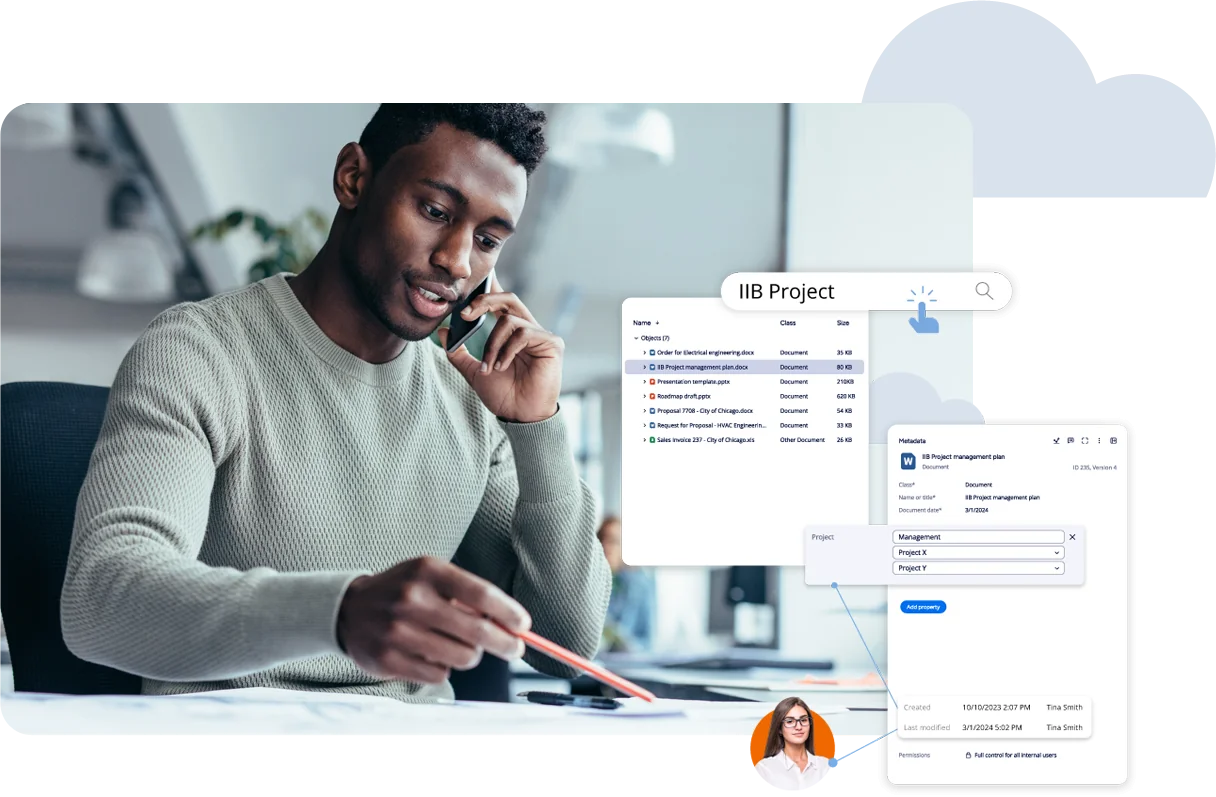
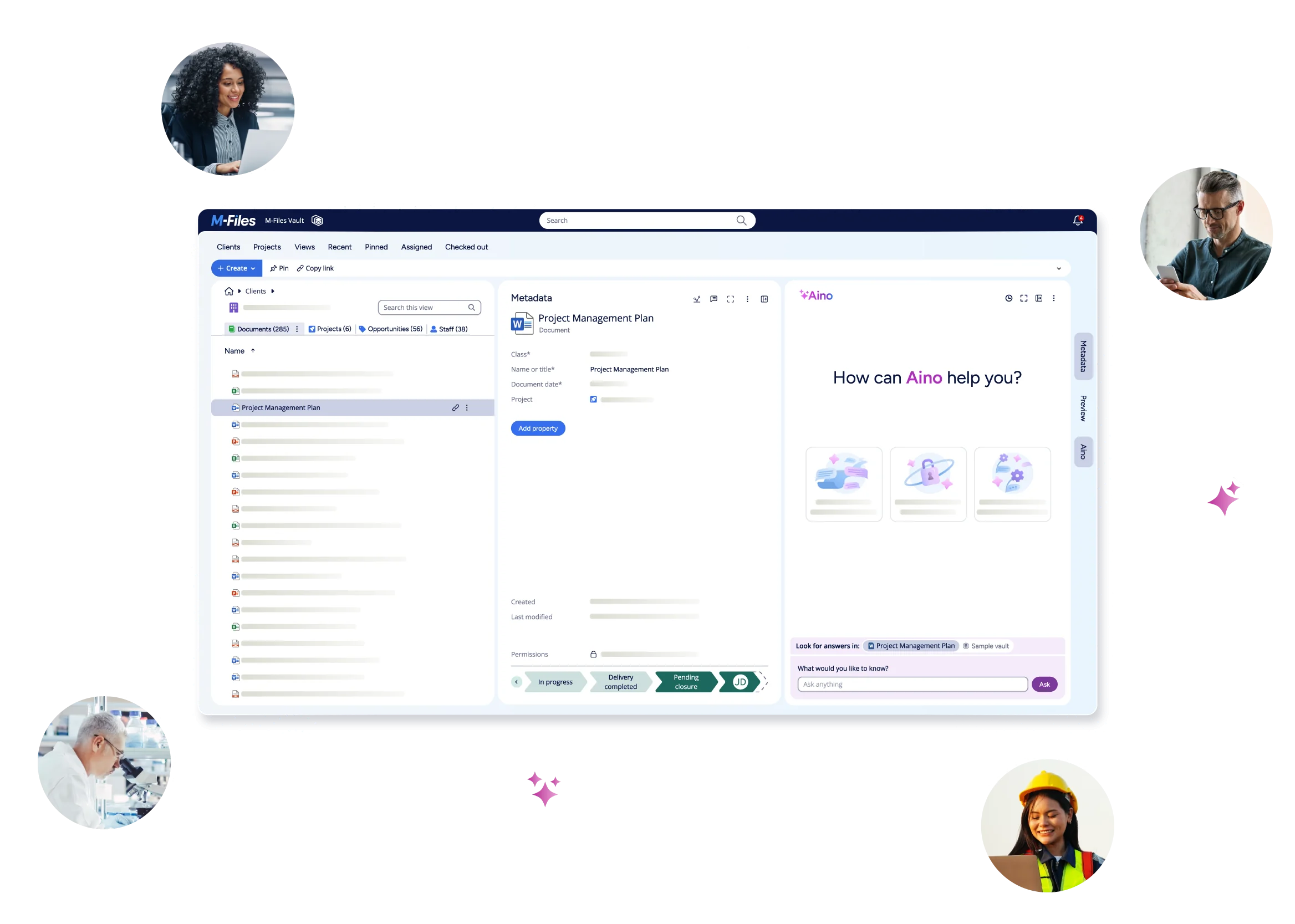
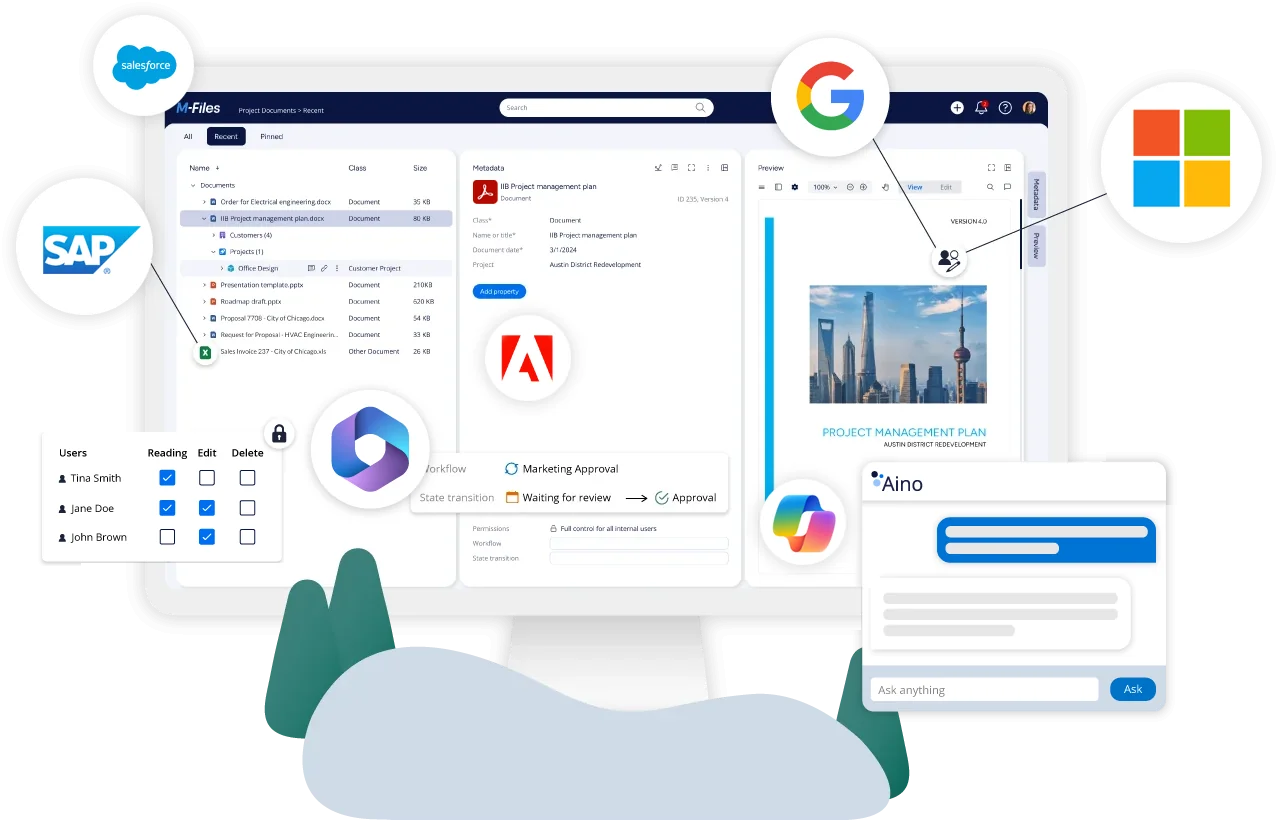
M-Files: An Intelligent Information Management Platform
M-Files simplifies the task of finding, accessing, and sharing documents with people inside and outside the organization. Powered by artificial intelligence, M-Files connects all documents and information across every platform and repository, analyzing them to determine their content and context. Rather than requiring documents to be migrated to a single repository, M-Files indexes, syncs, and maintains documents wherever they reside – on local drives, in the cloud, in email inboxes, within CRM systems, in network folders, in filesharing services, or in other business systems and storage locations.
By storing and retrieving documents based on metadata concerning what’s in the file rather than where it’s located, M-Files makes it easy to find everything with just a couple clicks. By storing a single copy of a file and providing links to those who need to access or edit it, M-Files creates a single source of truth and avoids versioning headaches. And by connecting to legacy systems and archives, M-Files data management technology provides a full view of data across systems and applications, surfacing business-critical files from "dark data" stores.
M-Files' Document Security Systems
M-Files' unique architecture and approach to document management provides the tools and infrastructure you need to achieve superior document security.
Services to Support Deployment, Training, and Business Growth
As you look to M-Files’ technology for document security, document management, or enterprise content management, take advantage of our experience with services that support your journey from project start to document lifecycle management.
Why Secure Documents with M-Files?
M-Files improves business performance by helping people find and use information more effectively. Built on artificial intelligence technologies, M-Files breaks down information silos by delivering an in-context experience for accessing and leveraging information that resides anywhere in your system. By connecting content with intelligent automation, we increase the productivity of knowledge workers, strengthen collaboration, enable business continuity, and ensure a seamless digital experience.
Our automated processes keep business moving by simplifying document intensive tasks, minimizing human error, and streamlining processes. With M-Files, information flows freely and securely throughout your organization, keeping business and timelines on track.
Easily adaptable and scalable for powerful customization and evolving needs, M-Files is the choice of thousands of organizations in more than 100 countries.

How M-Files Enables Efficiency for Your Business
Need More Information?
Refer to our Frequently Asked Questions (FAQs) section below:
Discover the Power of Artificial Intelligence Capabilities
Watch videos and access resources to learn how AI can transform your knowledge work with M-Files Aino.